Posted on 08/05/2022 4:25:17 PM PDT by FarCenter
DEF CON may be about to blow lid off security hole
The US government is warning of critical vulnerabilities in its Emergency Alert System (EAS) systems that, if exploited, could enable intruders to send fake alerts out over television, radio, and cable networks.
The Department of Homeland Security (DHS) said in an advisory it was recently informed about the flaws in EAS encoder and decoder devices, adding that they were successfully exploited by Ken Pyle, a security researcher at cybersecurity firm CYBIR. There is a sense of urgency to the advisory because the exploit "may" be presented, with proof of concept code, at the DEF CON conference in Las Vegas next week.
"In short, the vulnerability is public knowledge and will be demonstrated to a large audience in the coming weeks," the agency wrote in the advisory, which was issued this week by DHS' Federal Emergency Management Agency (FEMA).
The DHS is urging organizations that operate the EAS to ensure that their devices and supporting systems are updated with the most recent software versions and security patches, are protected by a firewall, and are monitored, with audit logs being regularly reviewed to ensure there is no unauthorized access.
The exact nature of the security flaws was not disclosed by Homeland Security. However, it's reported that the holes are present in the Monroe Electronics R189 One-Net DASDEC EAS device, and this can be remotely compromised to send out fake alerts, lock out legit users, and cause other damage.
EAS has far-reaching capabilities nationally and locally, though it's probably best known for the irritating regular tests that loudly interrupt TV and radio broadcasts. The service on the federal level is run by FEMA and its partners, including the Federal Communications Commission (FCC) and National Oceanic and Atmospheric Administration.
The system is designed to ensure that the president can address US citizens within 10 minutes during a national emergency and requires that radio and TV broadcasters, cable TV, wireless cable systems, satellite, and wireline operators ensure that can happen.
State and local officials also can use the system during emergencies, which can range from extreme weather events to AMBER alerts. The alerts are delivered via the Integrated Public Alert and Warning System (IPAWS).
Well, that’s just great.
It’s gone woke ?
Great idea to announce this to the World.
Yeah, it's Racist, Homophobic and doesn't use Green Energy, the Horror!.
I have no idea what's really going on, but I think it's not good.
I would also bet that there is no one named Ken Pyle. This feels like saying, "Osama Bin Laden was killed this morning by Tech Sgt John Smith who lives with his beloved family on Elm Street in Smalltown, Ohio."
Since when does the government identify people like this?
Well, the government is focused on the important issues — tracking down all the white supremacists, Trump terrorists, opening the southern border, etc. — that it doesn’t have time to deal with the minor things like national security.
Going the way of car alarms, wrong most of the time so no one pays any attention to them anymore anyhow.
If the exploit is going to be announced next week at the DefCon conference in Las Vegas, you kind of need to disclose it to get folks to patch their gear.
Whoops, the test you just heard would have been followed by a gigantic flash in the east as NY and DC are burned to a crisp. This concludes this test of the Emergency Alert System..
Fake News on a scale even CNN never envisioned! (and much higher ratings)
Once upon a time these alerts had get by humans who could verify if they were real or not.
Now this system is about as secure as us voting machines.
There seems to be a Ken Pyle. (Although I’ll admit to being at a meeting where a guy signed in with the last name of Undercoffer...)
https://www.rsaconference.com/experts/ken%20pyle
Ken Pyle is a partner of CYBIR, specializing in exploit development, penetration testing, and reverse engineering. As a highly rated and popular lecturer he has presented groundbreaking research at major industry events such as DEFCON, ShmooCon, Secureworld, HTCIA International, and others, focusing on fixing sets of problems that had been deemed unfixable or esoteric. He has discovered and published numerous critical software vulnerabilities in products from companies such as Cisco, Dell, Netgear, Sonicwall, HP, Datto, Kaseya, and ManageEngine, earning Multiple Hall of Fame acknowledgements. Pyle is a Graduate Professor of Cybersecurity at Chestnut Hill College. As an author, he has published several whitepapers and academic works on a wide range of topics.
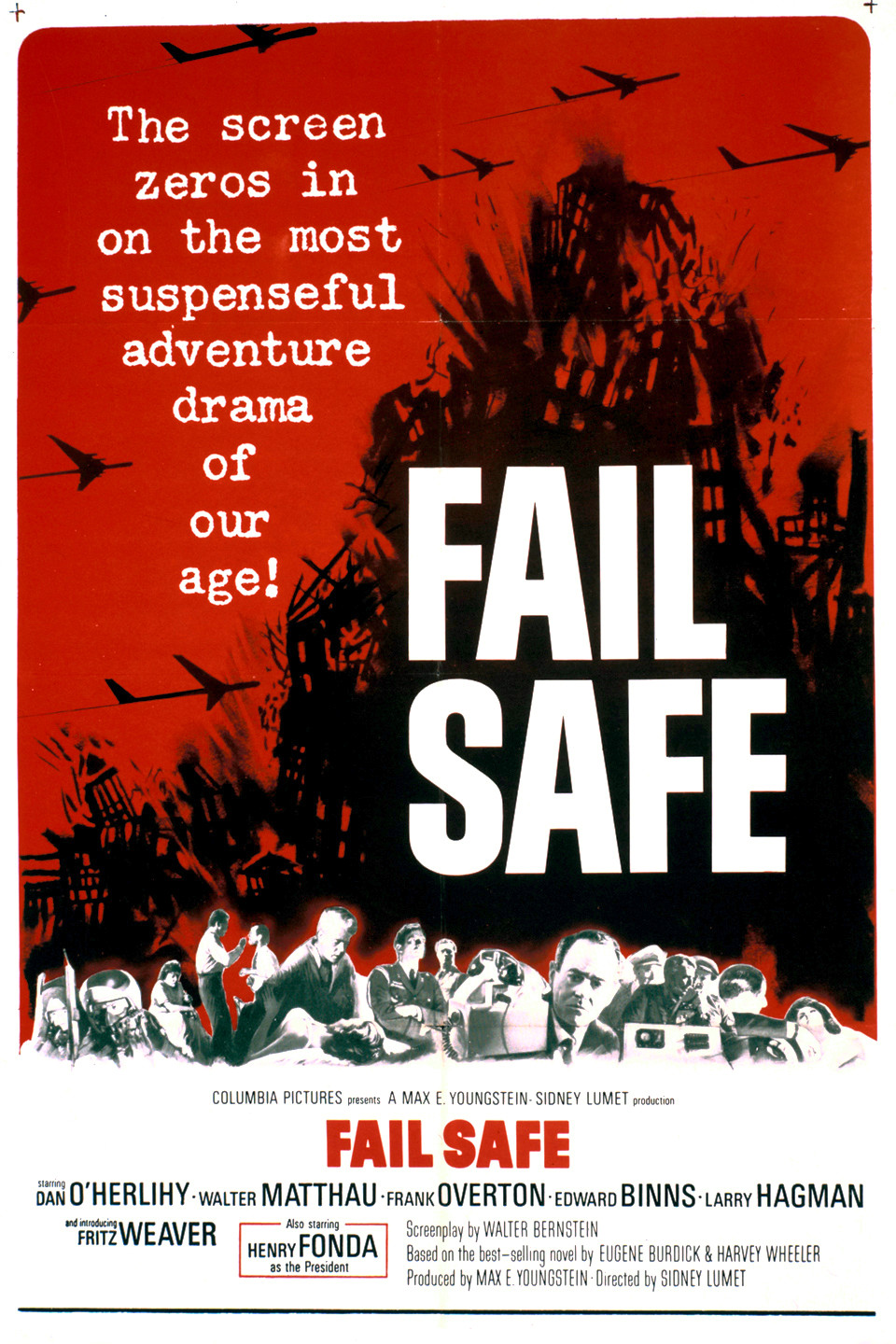
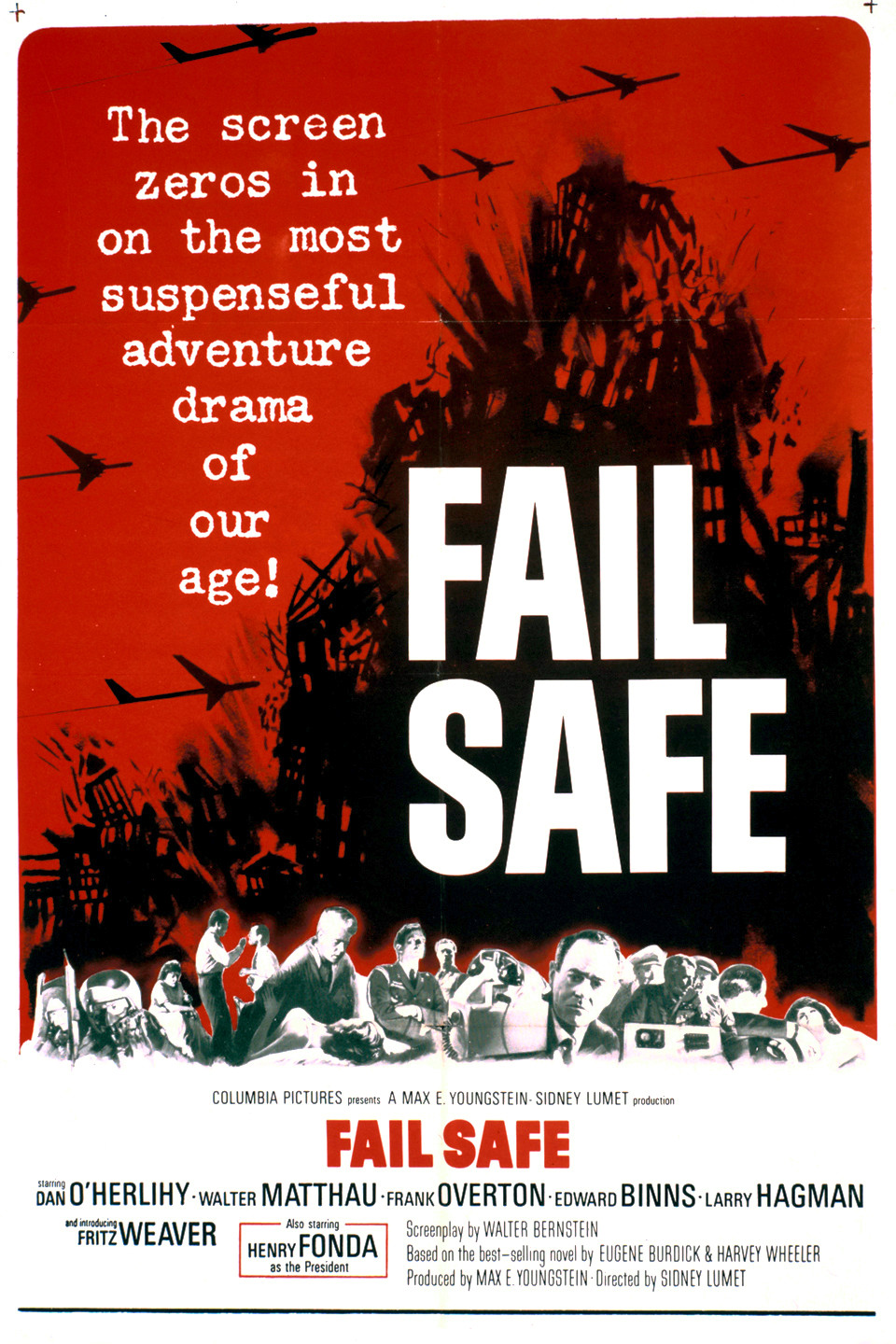
Harry Morgan, Harry Fonda and an extremely convincing Larry Hagman.
Great movie.
Sliding through the frequencies very fast (or was it quickly)
OK. Well, he has a security clearance, he’s really good at breaking into sensitive US systems and he knows a lot of stuff. Sure hope no one kidnaps him and gives him any enhanced interrogation.
Seems like poor OPSEC to put his name out there, but it’s not my problem.
NYC with an absurd nuclear tutorial too. This does not bode well.
The six B-58s taking off were the same plane. They just kept changing them zoom and possibly the angle. Maybe multiple cameras? 🎥
They snuck out to the fence to catch a B-58 lifting off.
4 - J-79s - ooh baby
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.