
Rich Skrenta today
Posted on 12/14/2012 10:15:57 AM PST by ShadowAce
To the author of Elk Cloner, the first computer virus to be released outside of the lab, it’s sad that, 30 years after the self-replicating code's appearance, the industry has yet to come up with a secure operating system.
When Rich Skrenta, created Elk Cloner as a prank in February 1982, he was a 15-year-old high school student with a precocious ability in programming and an overwhelming interest in computers. The boot sector virus was written for Apple II systems, the dominant home computers of the time, and infected floppy discs.
If an Apple II booted from an infected floppy disk, Elk Cloner became resident in the computer’s memory. Uninfected discs inserted into the same computer were given a dose of the malware just as soon as a user keyed in the command catalog for a list of files.
Infected computers would display a short poem, also written by Skrenta, on every fiftieth boot from an infected disk:
Elk Cloner: The program with a personality
It will get on all your disks It will infiltrate your chips Yes it's Cloner!
It will stick to you like glue It will modify ram too Send in the Cloner!
Elk Cloner, which played other, more subtle tricks every five boots, caused no real harm but managed to spread widely. Computer viruses had been created before, but Skrenta’s prank app was the first to spread in the wild, outside the computer system or network on which it was created.

Rich Skrenta today
“I was a geek and a computer nerd, interested in all aspects of technology,” he says. “I wanted to build a robot but there was no kit available and I had no mechanical skills. At elementary school, I used to experiment with vacuum tube radios but the slightest mistake during construction meant they didn’t work. I didn’t even find it easy putting together railway sets.”
“With programming I discovered a way to mimic things I saw in the movies,” Skrenta says, noting that some of his favourite films at the time were 2001: A Space Obyssey and Colossus: The Forbin Project.
“The physical stuff was frustrating by comparison,” he added.
Skrenta received an Apple II Computer as a Christmas gift in 1980. “It took over my life. I spent every waking hour immersed in computer games and programming.”
Skrenta wrote his own text-based adventure game, the opening of which placed the gamer into the role of a survivor of an airliner crash. This taught him to program in Basic and he later picked up assembly language skills.
The Apple II came with two floppy disk drives, and enthusiasts shared software and games through computer clubs. Software piracy was rife, and Skrenta was right in the middle of the scene.
“I was a member of a computer club in Pittsburg. I used to copy software and share it with friends. There was a thriving pirate software market and people used to exchange games and software on floppy discs,” he explains.
It was this that got him thinking about how he could use this mechanism to play tricks on his pals. He sometimes altered the floppy discs he shared with friends so that they would display on-screen messages or shut down thier computer.
“I decided to booby trap new games to put up a message,” he recalls. “I gave a floppy to one of the guys at the computer club, and it worked. At the time I though it was hysterically funny.
“I did a couple of more pranks before people wouldn't let me touch their discs any more.”
This got him thinking: could he alter the contents of a floppy disc without touching it? His experiments led him to develop program that would run in the background, checking for the presence of a new disk and, if it found one, could modify files stored on the disk.
The result of this work was a program that, in effect, was coded to hop from disk to disk, propagating itself from machine to machine. The first virus, Elk Cloner, was born.
“Tech books on hacking the Apple II covered system entry points, such as turning on the disc drive motor. One of the core applications, System Monitor, had holes in it. Elk Cloner used those holes.”
Elk Cloner took about two weeks to write in assembly language, Skrenta recalls. And if it’s mode of operation sounds simple, making it actually happen was quite a technical challenge. His earlier adventure game took longer but was more creative, like making a puzzle.
“It worked like a charm and spread all over the place,” Skrenta remembers with a chuckle. His cousins in Batimore and - years later, he discovered - a friend in the US Navy were among those whose computers caught the virus.
Not that there weren’t ways of avoiding infection.
“Elk Cloner created a rattling noise when the program started. If a disc was infected you could hear it. If you inserted an infected disc in an Apple II you can hear the head swoosh sound, an audible signature.
“It would infect a new disc if machine wasn’t rebooted. If an Apple II was rebooted every time, Elk Cloner wouldn’t have spread. But, given people computer habits, it spread like crazy,” Skrenta explained.
Friends may have cursed Skrenta and then, seeing the joke, chuckled at his antics, but not everyone was impressed by the humour or the programming skill he demonstrated. The first person to confront Skrenta about his antics was one of his teachers.
“The maths tutor confronted me as I was taking off my coat. He accused me of going into his office and hacking his computer,” Skrenta says. To this day, he doesn’t know who the teacher latched onto him as a likely suspect, figuring it was his clear enthusiasm for computers that gave the game away.
But, aside from the maths man, there was was “no major reaction” to Elk Cloner, something Skrenta viewed as a “silent victory”.
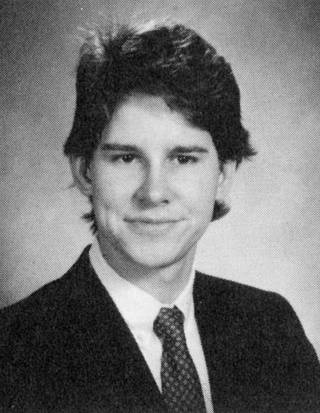
Rich Skrenta in 1989
Source: Northwestern University
“The virus is fairly harmless, had no network connectivity, and problems were solved by a reboot,” he says.
Skrenta created a utility to remove Elk Cloner from infected discs, again written in assembly language. He never thought of making this applications widely available. There was certainly no need for a more sophisticated Apple II malware scrubber since neither Skrenta nor anyone else created a virus for the platform.
He’d had his fun. “Elk Cloner was it for me and the virus world,” Skrenta explains.
Skrenta went on to study computer science at university where he had access to mainframe that had more memory and was obviously much faster than the Apple II. This was around the time MS-DOS machines became commonplace.
“I didn't want to own IBM PC and the next computer I had was a minicomputer running a version of Unix,” Skrenta remembers. He's since had some exposure to Windows machines and the computer virus that often infect them in recent years, much like anyone else.
Early malware for non-PC devices - Elk Cloner on the Apple II, BHP on the Commodore 64 - came five years before Brain, the first Windows PC virus, in 1986.
“PC are always going south with God knows what," Skrenta says. “So I’ve used Macs for the last few years.”
Not that he blithely accepts or trots out the line that Macs are somehow invulnerable to infection. “Macs have switched to a Unix core but there’s always a way in,” he admits. Indeed, the Flashback Trojan that used a Java exploit to infect Mac OS X machines earlier this year demonstrates that today’s virus writers - not jokers like Skrenta was - are targeting the platform.
Were they inspired by Skrenta’s work? Skrenta doesn’t think so. "I don't think [Elk Cloner] had any effect on subsequent malware development," he says. “The Brain virus was created by two brothers without any knowledge of Elk Cloner.”
Like Elk Cloner, the Brain virus, written by Pakistani brothers Basit and Amjad Alvi, was relatively harmless but spread widely. This proved to an exception to the general rule of subsequent malware development.
“Early on, all PC malware just infected floppies,” says Mikko Hypponen, CRO at Finnish anti-virus firm F-Secure. “Then we started seeing file infectors, infecting COM programs. They were still spreading between devices as they were carried on floppies.
“Things started changing quickly when the internet came around. First email worms [Anna Kournikova and Love Bug], then internet worms (Blaster, Slammer, Sasser, Code Red etc). And on to malware that's spread via exploits on websites, which is where we are today.”
Money-making with malware started just ten years ago. This brought banking Trojan, often developed with cybercrime toolkits such as ZeuS and SpyEye, and botnet agents to send spam or launch DDoS attacks from compromised hosts, into the picture. More recently, targeted Trojan attacks aimed at cyber-espionage, cyberweapons such as Stuxnet and Android malware have all become a headache.
Three decades after the creation of Elk Cloner, boot sector viruses remain a problem, says Hypponen, but he reckons their days may, at long last, be numbered.
“We've suffered from boot-level malware from the very beginning,” he said. “Elk Cloner, just like Brain and many of the early Apple and Mac viruses infected boot sectors. Arguably one of the most common examples of malware today, ZeroAccess, infects the boot sector of a Windows box.
“In all of these cases, the malware boots up first and then boots up the operating system after it has loaded itself. Hopefully the UEFI boot feature in Windows 8 will finally end this.”
Back in the early 1980s, references to Elk Cloner were few and far between. It wasn’t deemed worth of newspaper reports, for instance. But over the years it has become a bigger story. Skrenta role in the creation of the virus only came to wider attention after he wrote a letter to Scientific American on the subject, which led to a larger article in March 1985 on the (then not extensive) threat posed by computer malware.
“For the first ten years [Elk Cleaner] was a non event,” Skrenta admits.
Skrenta went on to work in computer security between 1995 to 1998, specifically on a cryptography project with Sun Microsystems, before continuing a successful career in information technology, most recently as the CEO of search engine start-up blekko.
Today, he reckons the industry has got its priorities wrong. “The anti-virus industry makes me sad,” he says. “We should build systems to be more resistant to computer viruses rather than have a multi-million dollar industry to do clean up.
“If more people knew about Elk Cloner at the time perhaps it would have led to more secure OS development.” ®


My husband insists that computer viruses are made and released by the same people who sell anti-viral software.
Historical significance aside, the “I want to see if I can do it” attitude, the “Let’s cause some havoc, it’ll be cool” attitude and all the other ‘prank’ viruses cause irreparable harm to people that depend a virus free medium to plan their lives, manage their money, and go about their life peacefully.
In my world, a person that is definitely determined to have promulgated a virus should be tried, convicted - and executed.
Your world is boring and not very innovative. It's that exact attitude that allowed the US to be the military and economic powerhouse that it is today.
“Computer viruses had been created before...”
“The first virus, Elk Cloner, was born.”
It’s definitely one or the other.
Well, if I remember, AppleII never booted from floppy. The whole OS was there on chip. But it used the floppy for other, non-boot, process.
The first “real” pc virus was Brain, an advertising stunt from a Pakistani.
So you condone it? Way to go.
Back in the days when viruses were simple pranks. One day back around 1992 my boss called me to his office. His computer was asking him to “Type Happy Birthday Joshi.” He had a silly boot sector virus that it turned out was on > 50% of the floppies in the company.
He didn’t appreciate the humor in it like I did, and I got yelled at for laughing.
I don’t know, every Apple II that I ever used booted from floppy and had no hard disk unless you connected an external one.
Booted from memory (chip) but had no disk system by default. Later, the 143k externals came and to load the disk routines it did a little poke at the physical disk out from the memory. I programmed a lot for the little bugger back in 1980 or so. And I have a couple of old Elks stuffed away among around 500 old bootvir floppies in an archival box.
Most of the houses have done that sort of thing. They will tell you that the AV virus writer is a myth. It is not. In my collection I have a lot of nasty stuff that is written by people on the inside, both known and unknown.
Eugene was never pushing viruses, but I remember him having at least one former writer.
Nah, too easy...I prefer these idiots be breaking rocks or clearing brush on chain-gangs. A few summers clearing trash off the sides of highways...that sort of thing. I'll bet most of them have never worked a hard physical day in their lives. I'd give them the opportunity to experience real hard work. A guy with a gun, a whip, and a big, ferocious dog watching them. And no computers in their cells.
I had a computer guy working for my shop in the early 90s and he wrote a virus in less than 30 minutes to show how easy it actually is.
Apple II ProDos was loaded from a “system disk.” The actual boot loader was burned into ROM but all it did was direct the primary disk drive head to Track 0 Sector 0 and start a load there, then JMP to the load-point address.
If I remember my Apple II internals ...
Naw
I’m thinking razor blades, salt, alcohol (for the administrator) sleep depredation and Rap Music (sorry that aint Music)
TT
Duct Tape and Castration but not in that order to shut them up for good.
Favorites of mine too.
Yes, that was the procedure - all disk handling had to start from the system disk. The rest of the operating system, like keyboard, display and Basic was on ROM.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.